4.43 If the new value v for x is larger, then we let v fall to a proper position in the subtree
rooted at x. Otherwise, we follow a path up the path from x to the root until we find a
proper position for the new value v. The pseudocode follows, where we assume that the
min-heap is implemented as a complete binary tree, and the parameter i is the index of
where x occurs in the tree. Clearly ChangePriority has O(logn) worst-case complexity.
//(j –1)/2 is a proper position for v
while j ≥ n .and. .not. Found do
if j < n – 1.and. A[j] < A[j + 1] then //then move to right child j + 1
j ← j + 1 //path finder updated to right child
endif
j ← (i – 1)/2
while j ≥ 0 .and. A[j] > v do
A[i] ← A[j] //move parent down one position in path
i ← j //move v up one position in path
j ← (j – 1)/2
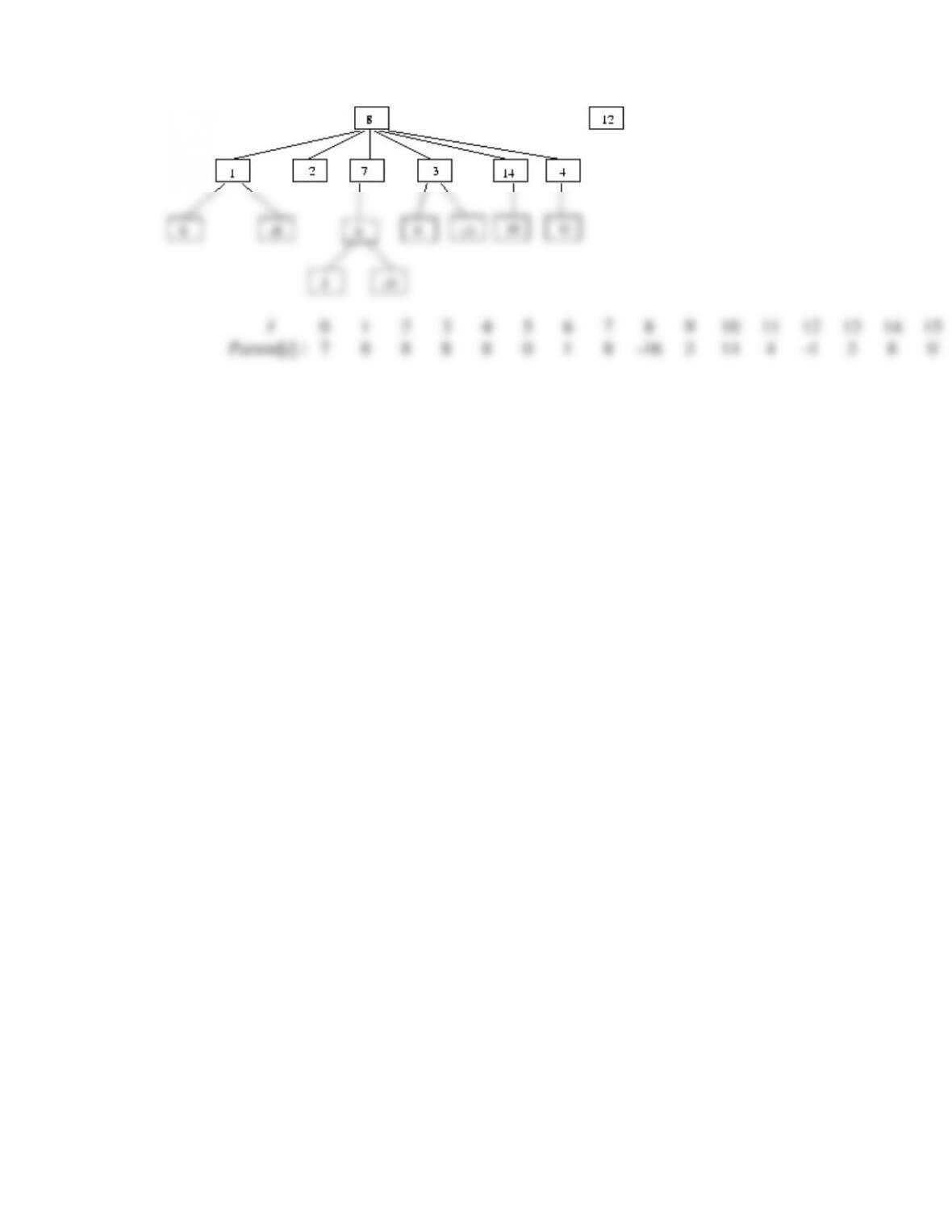
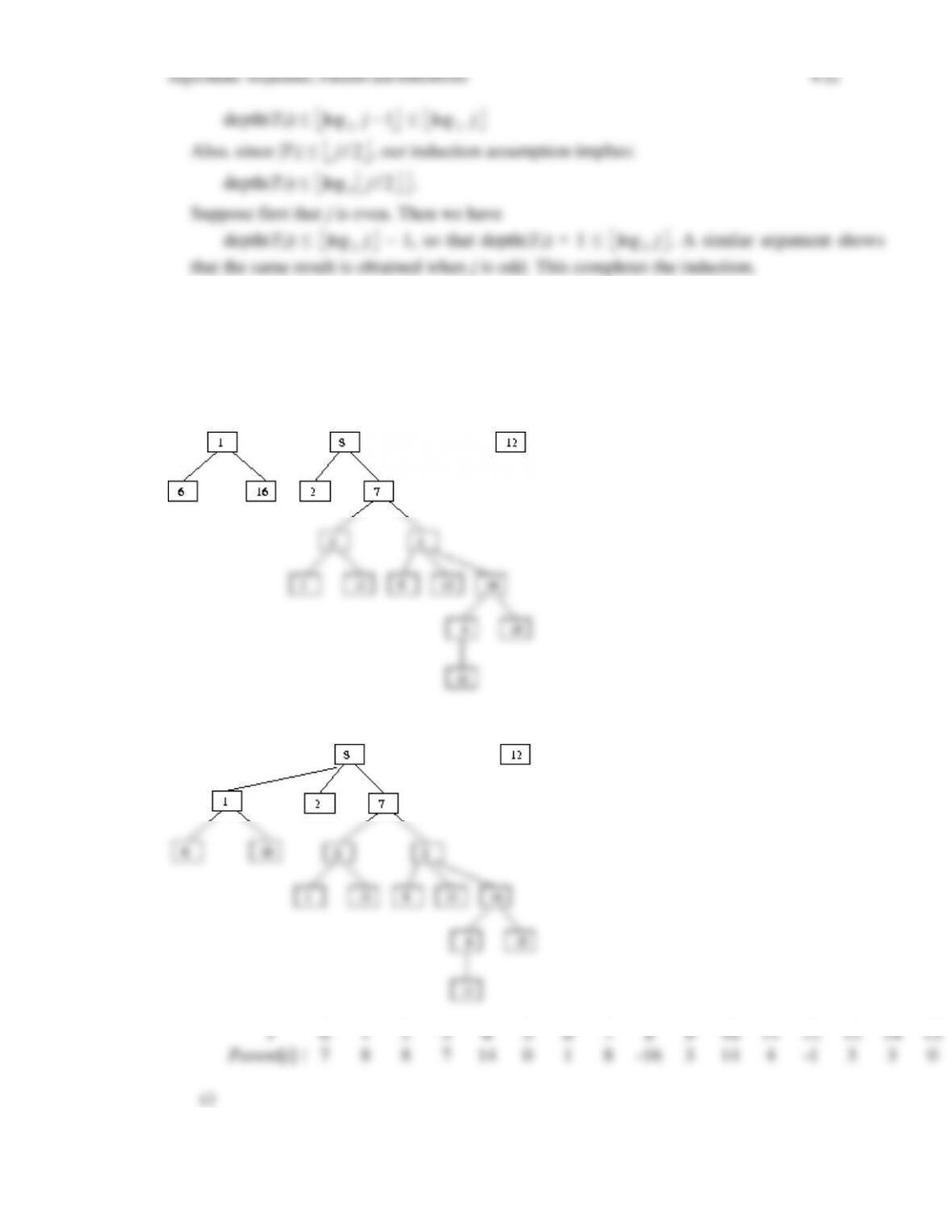
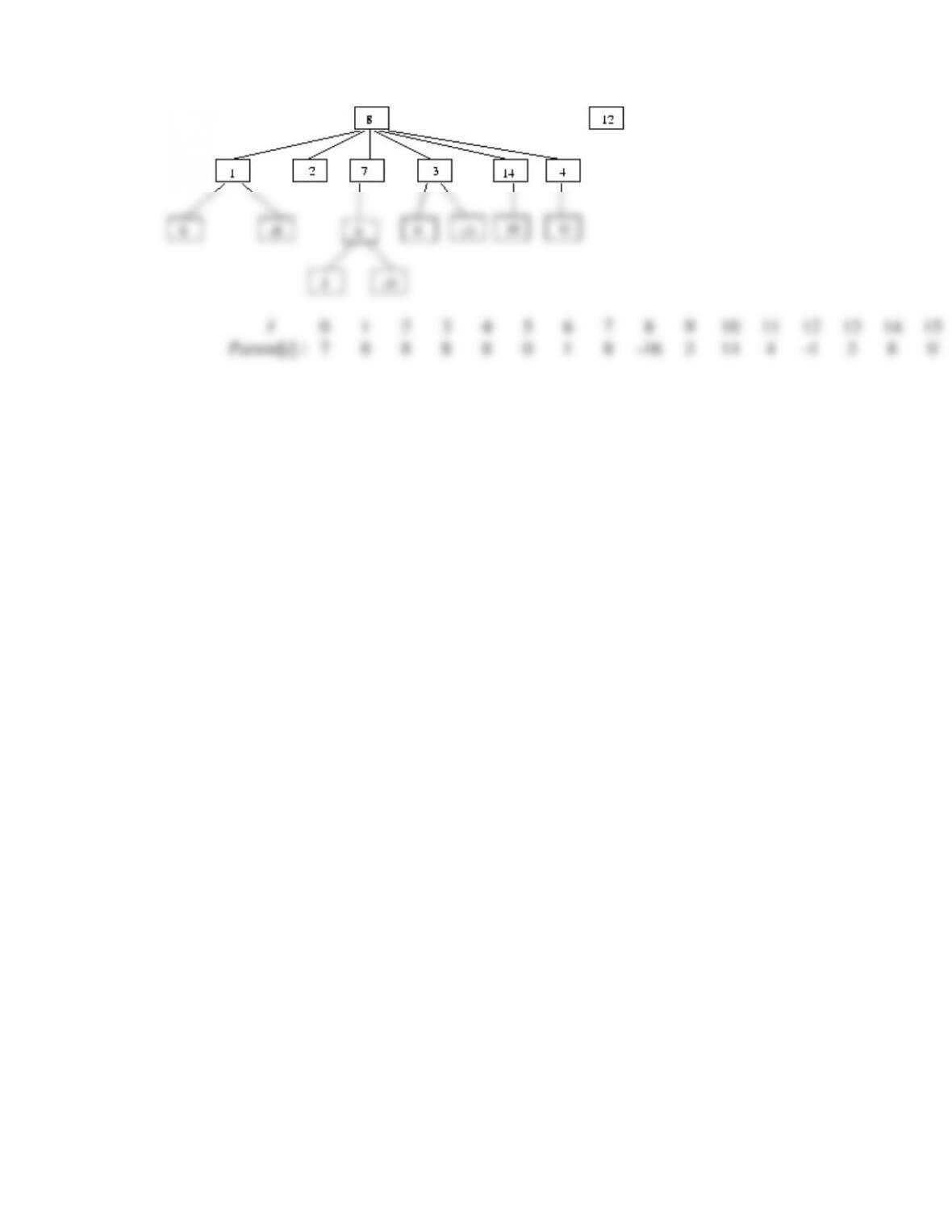
4.44 a) This exercise is a straightforward generalization of the array implementation of a
heap using a complete binary tree to using a complete k-ary tree. One merely notes that the
formula for the parent of a node with index i is given by
, whereas the children of